The Challenges of Modern Perimeter Security
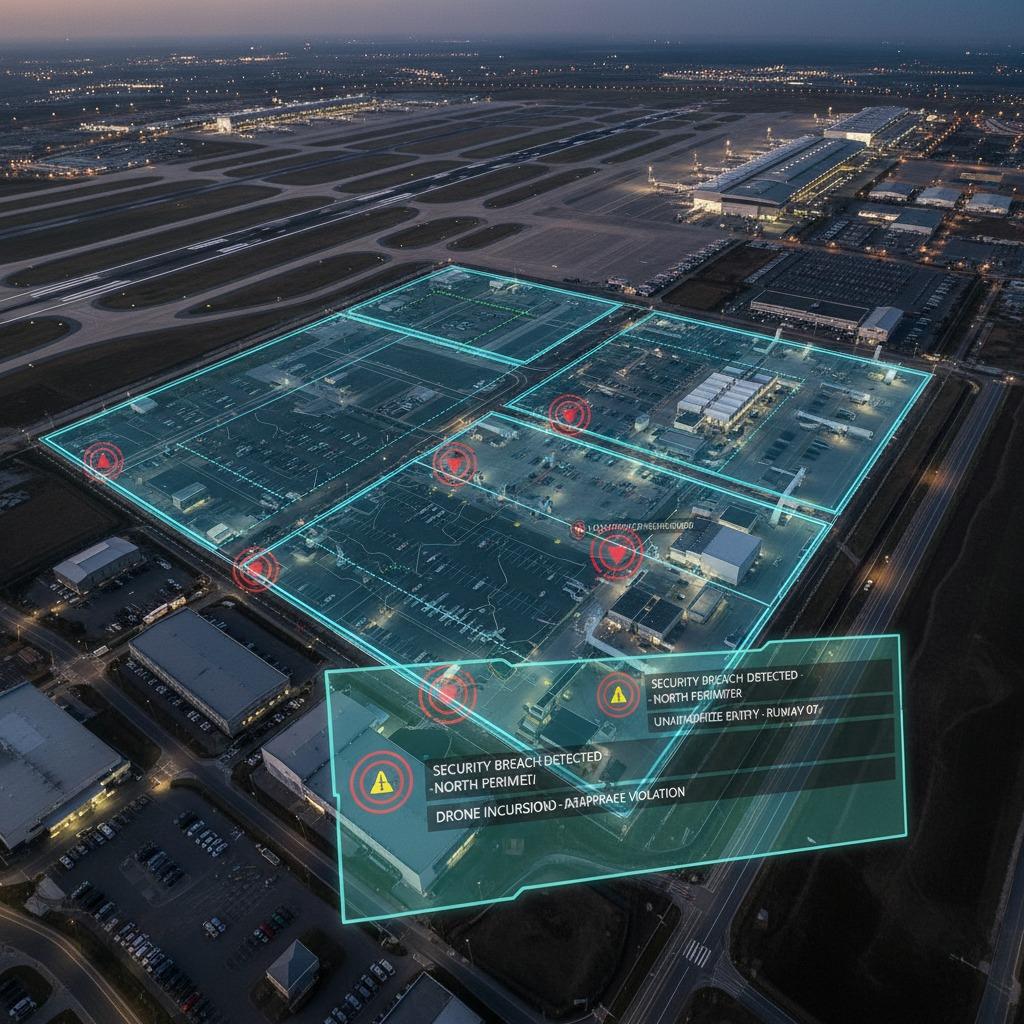
In today's rapidly evolving security landscape, traditional methods of protecting sensitive areas often fall short, especially when it comes to geofencing enforcement. Geofencing enforcement involves creating virtual boundaries that trigger alerts or actions when breached, but issues like unreliable detection in complex environments and vulnerabilities during signal disruptions pose significant problems. Facilities such as airports, military bases, and industrial sites face constant threats from unauthorized intrusions, where delayed responses can lead to catastrophic breaches. Without robust geofencing enforcement, organizations struggle to maintain airspace compliance and ensure safety, leaving them exposed to risks that escalate quickly.
Addressing Intruder Detection Gaps
One major hurdle in geofencing enforcement is effective intruder detection, where standard systems fail to distinguish between false alarms and genuine threats amid urban clutter or natural obstacles. To solve this, advanced geofencing enforcement solutions integrate multi-sensor fusion technologies, combining radar, optical cameras, and AI-driven analytics to achieve precise intruder detection. This approach not only minimizes false positives but also provides real-time monitoring, allowing security teams to respond proactively. By enhancing geofencing enforcement with these tools, organizations can safeguard their perimeters more reliably, turning potential vulnerabilities into fortified defenses.
Ensuring Fail-Safe Sensing for Continuous Protection
Fail-safe sensing is crucial for geofencing enforcement, yet many systems lack redundancy, leading to failures during critical moments like power outages or environmental interference. The solution lies in deploying resilient geofencing enforcement frameworks that incorporate backup sensors and automated failover mechanisms, ensuring uninterrupted operation. For instance, incorporating thermal imaging alongside primary detectors creates a fail-safe sensing layer that maintains vigilance even in adverse conditions. This not only bolsters overall security but also builds trust in the system's ability to protect assets without compromise, making geofencing enforcement a cornerstone of dependable defense strategies.
Navigating Airspace Compliance with Precision
Airspace compliance presents another challenge in geofencing enforcement, particularly for drone operations and aerial surveillance, where regulatory violations can result in hefty fines or operational shutdowns. Effective geofencing enforcement addresses this by embedding compliance algorithms that dynamically adjust virtual boundaries based on airspace regulations and real-time data from aviation authorities. Integrating geofencing enforcement with drone management software ensures that all flights adhere to no-fly zones, promoting seamless operations while avoiding legal pitfalls. This targeted solution empowers organizations to operate within bounds, enhancing safety and regulatory adherence in increasingly regulated skies.
Achieving Reliability Under GNSS-Denied Conditions
Finally, reliability under GNSS-denied conditions—such as in jammed or indoor environments—undermines the effectiveness of geofencing enforcement, where GPS signals are essential for boundary definition. To overcome this, innovative geofencing enforcement systems leverage alternative positioning technologies like inertial navigation and ultra-wideband (UWB) sensors, providing accurate localization without satellite dependency. These enhancements ensure that geofencing enforcement remains operational in hostile or signal-blocked scenarios, offering a comprehensive shield against sophisticated threats. By prioritizing reliability under GNSS-denied conditions, security setups become more versatile and future-proof, addressing the full spectrum of modern challenges.
In summary, implementing advanced geofencing enforcement with integrated intruder detection, fail-safe sensing, airspace compliance, and GNSS-resilient features transforms perimeter security from reactive to proactive. Organizations adopting these solutions not only mitigate risks but also gain a competitive edge in safeguarding their operations effectively.



